Linux and Unix security solutions
Security auditing, system hardening, and compliance monitoring
Lynis Enterprise performs security scanning for Linux, macOS, and Unix systems. It helps you discover and solve issues quickly, so you can focus on your business and projects again.
Want to scan your first system, within just 1 minute? Start with the open source tool Lynis.
Benefits
- Easy to use interface
- Integration with other tools
- Understandable reports
- Easy set-up, low maintenance
- Audits within only a few minutes
- Focused on automation
- Specialized in Unix technology
- Independent of age and version
Lynis is a great tool to test our baselines and identify current problems and gaps
Dolev Farhi - DevOps Engineer, Paytm labs (before: F5 Networks)
Product features
 In-depth audits by host based scanning
In-depth audits by host based scanning Installation is optional
Installation is optional Even dependencies are optional
Even dependencies are optional All Unix, Linux, BSD and macOS versions
All Unix, Linux, BSD and macOS versions Free community version available
Free community version available Action plans, with priority based hardening strategies
Action plans, with priority based hardening strategies Find undiscovered vulnerabilities
Find undiscovered vulnerabilities
 Compliance testing (PCI, HIPAA, SOx and others)
Compliance testing (PCI, HIPAA, SOx and others) Detect intruders and monitor for configuration issues
Detect intruders and monitor for configuration issues Continuous auditing, discover changes
Continuous auditing, discover changes Layered dashboards (technical and managerial)
Layered dashboards (technical and managerial) Reporting and data export
Reporting and data export Different levels of user access
Different levels of user access Open source software
Open source software
Experience it yourself
The best way to learn about the software is to try it yourself. Our suggested route:
- Start using the free and open source tool Lynis.
- Learn more about the plugins, extending the functionality of the tool.
- Upgrade to Lynis Enterprise. See the solutions page for details.
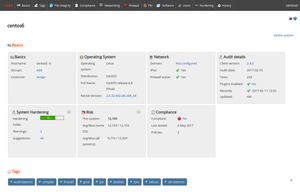
Click on the image above for a demo and request a trial.
 TechRepublic considers Lynis to be a must-use tool.
TechRepublic considers Lynis to be a must-use tool.
